Shell/Fingerprints: Unterschied zwischen den Versionen
imported>Burghardt |
imported>Gtest2 |
||
| (13 dazwischenliegende Versionen von 4 Benutzern werden nicht angezeigt) | |||
| Zeile 2: | Zeile 2: | ||
* Back to [[Shell]] |
* Back to [[Shell]] |
||
| + | To verify a fingerprint you need to know the correct one first. These to-be-verified correct fingerprints can be shown ''after'' you're logged in on the target server. Of course this is a classic chicken-and-egg problem. '''You need to get the correct fingerprints through an independent communication channel in beforehand.''' In our case that is the list below: |
||
| + | == Current fingerprints as of October 2017 == |
||
| − | While older ssh-versions relied on [[MD5]] (Message Digest number five) for generating a fingerprint this is considered "unsafe" for some time now. The current implementation uses [[SHA256]] by default. |
||
| + | <small>...verified to be valid in August 2019</small> |
||
| + | * '''sha256''': |
||
| − | == Current fingerprints as of April 2017 == |
||
| − | |||
| − | === Older Servers === |
||
| − | Included in [[debian]] [[Jessie]], [[Ubuntu]] [[Trusty]] and others. Used ''prior April 10th'' in <tt>login</tt>, <tt>shell</tt> and all pool workstations: |
||
<pre> |
<pre> |
||
| − | ~$ |
+ | ~$ for F in /etc/ssh/*.pub ; do echo -e "\n$F:"; ssh-keygen -l -E sha256 -f $F; done |
| − | Description: Ubuntu 14.04.5 LTS |
||
/etc/ssh/ssh_host_ecdsa.pub: |
/etc/ssh/ssh_host_ecdsa.pub: |
||
| − | 256 |
+ | 256 SHA256:L+FCMj2bm8x/BfR8AdaaLnqTmFD35D0EYNlFG7a2dt8 root@nfsadm (ECDSA) |
/etc/ssh/ssh_host_ed25519_key.pub: |
/etc/ssh/ssh_host_ed25519_key.pub: |
||
| − | 256 |
+ | 256 SHA256:H4FLNG2aNYRZ3jxepIx5E0s0a2ZvtZbbmVLt56b+nK0 root@nfsadm (ED25519) |
/etc/ssh/ssh_host_rsa_key.pub: |
/etc/ssh/ssh_host_rsa_key.pub: |
||
| − | 2048 |
+ | 2048 SHA256:DpP5/EfbApVUwseVeQOVpAFvGiZIJmYmjUyC4Cnuatk root@nfsadm (RSA) |
</pre> |
</pre> |
||
| + | * '''md5''' is officially deprecated but better than nothing: |
||
| − | === Newer Servers === |
||
| − | Included in debian [[Stretch]], Ubuntu [[Xenial]] and others. ''Currently used'' in <tt>login</tt>, <tt>shell</tt> and all pool workstations: |
||
<pre> |
<pre> |
||
| − | ~$ |
+ | ~$ for F in /etc/ssh/*.pub ; do echo -e "\n$F:"; ssh-keygen -l -E md5 -f $F; done |
| − | Description: Ubuntu 16.04.2 LTS |
||
| − | /etc/ssh/ |
+ | /etc/ssh/ssh_host_ecdsa.pub: |
| + | 256 MD5:07:84:c9:e1:59:4f:03:75:69:b1:e4:d0:b4:1f:9a:cd root@nfsadm (ECDSA) |
||
| − | 1024 SHA256:OpBcTf2pc3p3oUXKZvJ2773TULj6lskxYI/INZvLes8 root@c043 (DSA) |
||
| − | |||
| − | /etc/ssh/ssh_host_ecdsa_key.pub: |
||
| − | 256 SHA256:IN1YJYjBWzm1irujENh5KVB6RxqXBGbvIT6WrGv++fw root@nfs (ECDSA) |
||
/etc/ssh/ssh_host_ed25519_key.pub: |
/etc/ssh/ssh_host_ed25519_key.pub: |
||
| − | 256 |
+ | 256 MD5:93:11:29:c4:a2:03:e1:2d:b1:82:05:74:dd:a5:3b:9a root@nfsadm (ED25519) |
/etc/ssh/ssh_host_rsa_key.pub: |
/etc/ssh/ssh_host_rsa_key.pub: |
||
| + | 2048 MD5:de:db:6e:72:52:de:30:73:db:bb:6e:79:df:f9:2c:0d root@nfsadm (RSA) |
||
| − | 1024 SHA256:f7orU3tn+mVuMlv/CjnfJOF8dr4/VhPhZMtSirMIndQ root@c043 (RSA) |
||
</pre> |
</pre> |
||
| + | == Actually compare a fingerprint when establishing a session == |
||
| − | If you are using an old client you need to check the deprecated MD5 checksum: |
||
| + | |||
| + | Older implementations (for example from debian Jessie) use md5 - without explicitly stating this fact: |
||
<pre> |
<pre> |
||
| + | ~$ ssh -o VisualHostKey=yes shell.informatik.uni-goettingen.de |
||
| − | ~$ lsb_release -d; for F in /etc/ssh/*.pub ; do echo -e "\n$F:"; ssh-keygen -l -E MD5 -f $F; done |
||
| + | The authenticity of host 'shell.informatik.uni-goettingen.de (134.76.81.100)' can't be established. |
||
| − | Description: Ubuntu 16.04.2 LTS |
||
| + | ECDSA key fingerprint is 07:84:c9:e1:59:4f:03:75:69:b1:e4:d0:b4:1f:9a:cd. |
||
| + | +---[ECDSA 256]---+ |
||
| + | | ..++o=o=o | |
||
| + | | .++ o *+o | |
||
| + | | o . ..+ . | |
||
| + | | . * . | |
||
| + | | S . o E | |
||
| + | | . | |
||
| + | | | |
||
| + | | | |
||
| + | | | |
||
| + | +-----------------+ |
||
| + | </pre> |
||
| + | Newer version (e.g. from Ubuntu Xenial) use sha256 by default: |
||
| − | /etc/ssh/ssh_host_dsa_key.pub: |
||
| + | <pre> |
||
| − | 1024 MD5:c0:e6:ac:3f:62:4c:4e:dc:cc:68:66:45:83:f2:23:9a root@c043 (DSA) |
||
| + | ~$ ssh -o VisualHostKey=yes shell.informatik.uni-goettingen.de |
||
| + | The authenticity of host 'shell.informatik.uni-goettingen.de (134.76.81.100)' can't be established. |
||
| + | ECDSA key fingerprint is SHA256:L+FCMj2bm8x/BfR8AdaaLnqTmFD35D0EYNlFG7a2dt8. |
||
| + | +---[ECDSA 256]---+ |
||
| + | | o+o== | |
||
| + | | .o.o.o+ | |
||
| + | | . o ++. | |
||
| + | | . . o *.o. | |
||
| + | | o +.S. * +o .| |
||
| + | | +.= o. =.o.o| |
||
| + | | +.o+.+ .E| |
||
| + | | o ++.= | |
||
| + | | =..o . | |
||
| + | +----[SHA256]-----+ |
||
| + | </pre> |
||
| + | On those newer ssh-clients you can request a specific algorithm to be used: |
||
| − | /etc/ssh/ssh_host_ecdsa_key.pub: |
||
| + | <pre> |
||
| − | 256 MD5:1a:04:8e:f5:7e:e6:44:6a:a8:1f:b7:f0:8c:40:f8:ff root@nfs (ECDSA) |
||
| + | ~$ ssh -o VisualHostKey=yes -o FingerprintHash=md5 shell.informatik.uni-goettingen.deHost |
||
| − | |||
| + | key fingerprint is MD5:07:84:c9:e1:59:4f:03:75:69:b1:e4:d0:b4:1f:9a:cd |
||
| − | /etc/ssh/ssh_host_ed25519_key.pub: |
||
| + | +---[ECDSA 256]---+ |
||
| − | 256 MD5:c5:fb:87:6c:78:29:32:90:ea:3d:3c:0d:9b:2c:83:bd root@c009 (ED25519) |
||
| + | | ..++o=o=o | |
||
| − | |||
| + | | .++ o *+o | |
||
| − | /etc/ssh/ssh_host_rsa_key.pub: |
||
| + | | o . ..+ . | |
||
| − | 1024 MD5:c6:82:13:00:60:c5:70:a7:60:6b:09:8d:c7:0b:b3:06 root@c043 (RSA) |
||
| + | | . * . | |
||
| + | | S . o E | |
||
| + | | . | |
||
| + | | | |
||
| + | | | |
||
| + | | | |
||
| + | +------[MD5]------+ |
||
</pre> |
</pre> |
||
| + | Note that older implementations just don't know "<tt>-o FingerprintHash</tt>" and will generate an error message only. That's the reason we list both old and new fingerprints above... |
||
| − | == Actually compare a fingerprint when establishing a session == |
||
| − | As a client you need to verify the actually used key/fingerprint to those documented above. Depending on old/new implementations the exact behavior and output might be different: |
||
| − | === Using an '''older''' client === |
||
| − | * connecting to an '''old''' server |
||
| − | ~$ ssh -o VisualHostKey=yes shell.informatik.uni-goettingen.de |
||
| − | Host key fingerprint is 07:84:c9:e1:59:4f:03:75:69:b1:e4:d0:b4:1f:9a:cd |
||
| + | === Windows === |
||
| − | * connecting to a '''newer''' server |
||
| + | [[PuTTY]] on windows looks like this: |
||
| − | ~$ ssh -o VisualHostKey=yes newerserverinstance.informatik.uni-goettingen |
||
| − | Host key fingerprint is 1a:04:8e:f5:7e:e6:44:6a:a8:1f:b7:f0:8c:40:f8:ff |
||
| + | [[Datei:putty-login+fingerprint.png|479px]] |
||
| + | Suprisingly Windows includes an SSH-Client meanwhile. You may omit the installation of PuTTY and just do: |
||
| − | === Using a '''newer''' client === |
||
| − | * connecting to an '''old''' server |
||
| − | ~$ ssh -o VisualHostKey=yes shell.informatik.uni-goettingen.de |
||
| − | Host key fingerprint is SHA256:L+FCMj2bm8x/BfR8AdaaLnqTmFD35D0EYNlFG7a2dt8 |
||
| + | P:\>cmd /v |
||
| − | * connecting to an '''old''' server |
||
| + | Microsoft Windows [Version 10.0.17763.615] |
||
| − | ~$ ssh -o VisualHostKey=yes -o fingerprinthash=md5 shell.informatik.uni-goettingen.de |
||
| + | (c) 2018 Microsoft Corporation. Alle Rechte vorbehalten. |
||
| − | Host key fingerprint is MD5:07:84:c9:e1:59:4f:03:75:69:b1:e4:d0:b4:1f:9a:cd |
||
| + | P:\>ssh -V |
||
| − | * connecting to a '''newer''' server |
||
| + | OpenSSH_for_Windows_7.7p1, LibreSSL 2.6.5 |
||
| − | ~$ ssh -o VisualHostKey=yes localhost |
||
| − | Host key fingerprint is SHA256:IN1YJYjBWzm1irujENh5KVB6RxqXBGbvIT6WrGv++fw |
||
| + | P:\>ssh username@shell.informatik.uni-goettingen.de |
||
| + | The authenticity of host 'shell.informatik.uni-goettingen.de (134.76.81.100)' can't be established. |
||
| + | ECDSA key fingerprint is SHA256:L+FCMj2bm8x/BfR8AdaaLnqTmFD35D0EYNlFG7a2dt8. |
||
| + | Are you sure you want to continue connecting (yes/no)? yes |
||
| + | Warning: Permanently added 'shell.informatik.uni-goettingen.de,134.76.81.100' (ECDSA) to the list of known hosts. |
||
| + | ####### |
||
| + | ####### shell.stud.informatik.uni-goettingen.de - login vm: shell5.cip.loc |
||
| + | ... |
||
== See also == |
== See also == |
||
Aktuelle Version vom 8. August 2019, 09:48 Uhr
- Back to Shell
To verify a fingerprint you need to know the correct one first. These to-be-verified correct fingerprints can be shown after you're logged in on the target server. Of course this is a classic chicken-and-egg problem. You need to get the correct fingerprints through an independent communication channel in beforehand. In our case that is the list below:
Current fingerprints as of October 2017
...verified to be valid in August 2019
- sha256:
~$ for F in /etc/ssh/*.pub ; do echo -e "\n$F:"; ssh-keygen -l -E sha256 -f $F; done /etc/ssh/ssh_host_ecdsa.pub: 256 SHA256:L+FCMj2bm8x/BfR8AdaaLnqTmFD35D0EYNlFG7a2dt8 root@nfsadm (ECDSA) /etc/ssh/ssh_host_ed25519_key.pub: 256 SHA256:H4FLNG2aNYRZ3jxepIx5E0s0a2ZvtZbbmVLt56b+nK0 root@nfsadm (ED25519) /etc/ssh/ssh_host_rsa_key.pub: 2048 SHA256:DpP5/EfbApVUwseVeQOVpAFvGiZIJmYmjUyC4Cnuatk root@nfsadm (RSA)
- md5 is officially deprecated but better than nothing:
~$ for F in /etc/ssh/*.pub ; do echo -e "\n$F:"; ssh-keygen -l -E md5 -f $F; done /etc/ssh/ssh_host_ecdsa.pub: 256 MD5:07:84:c9:e1:59:4f:03:75:69:b1:e4:d0:b4:1f:9a:cd root@nfsadm (ECDSA) /etc/ssh/ssh_host_ed25519_key.pub: 256 MD5:93:11:29:c4:a2:03:e1:2d:b1:82:05:74:dd:a5:3b:9a root@nfsadm (ED25519) /etc/ssh/ssh_host_rsa_key.pub: 2048 MD5:de:db:6e:72:52:de:30:73:db:bb:6e:79:df:f9:2c:0d root@nfsadm (RSA)
Actually compare a fingerprint when establishing a session
Older implementations (for example from debian Jessie) use md5 - without explicitly stating this fact:
~$ ssh -o VisualHostKey=yes shell.informatik.uni-goettingen.de The authenticity of host 'shell.informatik.uni-goettingen.de (134.76.81.100)' can't be established. ECDSA key fingerprint is 07:84:c9:e1:59:4f:03:75:69:b1:e4:d0:b4:1f:9a:cd. +---[ECDSA 256]---+ | ..++o=o=o | | .++ o *+o | | o . ..+ . | | . * . | | S . o E | | . | | | | | | | +-----------------+
Newer version (e.g. from Ubuntu Xenial) use sha256 by default:
~$ ssh -o VisualHostKey=yes shell.informatik.uni-goettingen.de The authenticity of host 'shell.informatik.uni-goettingen.de (134.76.81.100)' can't be established. ECDSA key fingerprint is SHA256:L+FCMj2bm8x/BfR8AdaaLnqTmFD35D0EYNlFG7a2dt8. +---[ECDSA 256]---+ | o+o== | | .o.o.o+ | | . o ++. | | . . o *.o. | | o +.S. * +o .| | +.= o. =.o.o| | +.o+.+ .E| | o ++.= | | =..o . | +----[SHA256]-----+
On those newer ssh-clients you can request a specific algorithm to be used:
~$ ssh -o VisualHostKey=yes -o FingerprintHash=md5 shell.informatik.uni-goettingen.deHost key fingerprint is MD5:07:84:c9:e1:59:4f:03:75:69:b1:e4:d0:b4:1f:9a:cd +---[ECDSA 256]---+ | ..++o=o=o | | .++ o *+o | | o . ..+ . | | . * . | | S . o E | | . | | | | | | | +------[MD5]------+
Note that older implementations just don't know "-o FingerprintHash" and will generate an error message only. That's the reason we list both old and new fingerprints above...
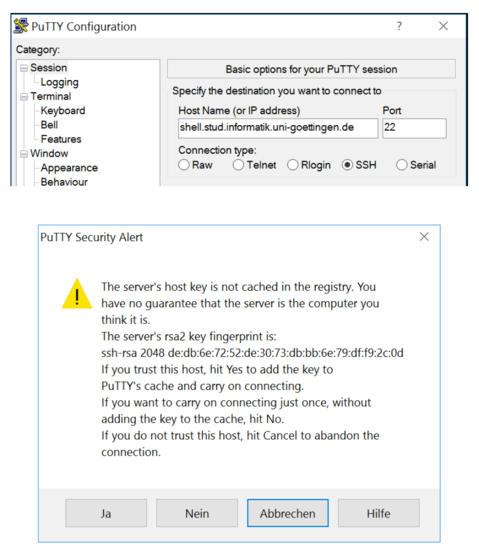
Windows
PuTTY on windows looks like this:
Suprisingly Windows includes an SSH-Client meanwhile. You may omit the installation of PuTTY and just do:
P:\>cmd /v Microsoft Windows [Version 10.0.17763.615] (c) 2018 Microsoft Corporation. Alle Rechte vorbehalten.
P:\>ssh -V OpenSSH_for_Windows_7.7p1, LibreSSL 2.6.5
P:\>ssh username@shell.informatik.uni-goettingen.de The authenticity of host 'shell.informatik.uni-goettingen.de (134.76.81.100)' can't be established. ECDSA key fingerprint is SHA256:L+FCMj2bm8x/BfR8AdaaLnqTmFD35D0EYNlFG7a2dt8. Are you sure you want to continue connecting (yes/no)? yes Warning: Permanently added 'shell.informatik.uni-goettingen.de,134.76.81.100' (ECDSA) to the list of known hosts. ####### ####### shell.stud.informatik.uni-goettingen.de - login vm: shell5.cip.loc ...