Shell: Unterschied zwischen den Versionen
imported>Burghardt |
imported>Burghardt |
||
| Zeile 96: | Zeile 96: | ||
* <tt>telnet</tt> is included in Windows also. But it is not ''installed'' by default. You need to activate it through "Windows-Features aktivieren oder deaktivieren"/"Add windows features" --> "Telnet-Client". You need Administrator privileges for this. So this is not an option on foreign computers |
* <tt>telnet</tt> is included in Windows also. But it is not ''installed'' by default. You need to activate it through "Windows-Features aktivieren oder deaktivieren"/"Add windows features" --> "Telnet-Client". You need Administrator privileges for this. So this is not an option on foreign computers |
||
| − | * There are dedicated tools available for this purpose. This one is tested and found to work as expected: https://sourceforge.net/projects/knockknock/ <br />The zip-file contains a ( |
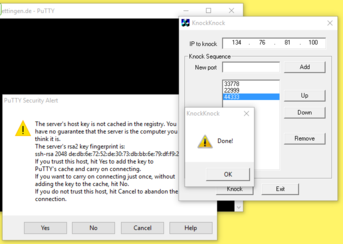
+ | * There are dedicated tools available for this purpose. This one is tested and found to work as expected: https://sourceforge.net/projects/knockknock/ <br />The zip-file contains a (surprisingly small) executable. It is usable without installation so you do ''not'' need Admin privileges |
* Use a web browser to tickle those ports |
* Use a web browser to tickle those ports |
||
Version vom 9. Juni 2016, 06:56 Uhr
 |
Beta Test. Please give feedback. Most important: Shell#Port_knocking |

|
Usage
Please read Shell#Port_knocking if you can not connect.
Simply use SSH to login to this machine:
ssh user@shell.stud.informatik.uni-goettingen.de
Note that the intially presented banner contains something like
####### shell.stud.informatik.uni-goettingen.de - login vm: shell5.cip.loc
...telling you the actual local name of the automatically chosen destination machine.
For Windows: use PuTTY (simple) or Cygwin (more complex and powerful) or any other SSH-implementation.
Target audience
These machines are meant to be used by students. But of course they can be used by any staff members! (For first time users: the only requirement is to logon one single time using one of the (physical) pool computers in our building - this will make you a "known user" to our systems.)
Load Balancing
This term is misleading on this specific installation: the default algorithm being used is simply "round-robin" - you'll get connected to the "next" machine one after another. If you landed on an overcrowded system simply disconnect/reconnect to use another machine.
Legacy login.stud
Both login.stud.informatik.uni-goettingen.de and login.informatik.uni-goettingen.de (for staff only) are not affected by this new approach. These "old" machines will continue to work unmodified.
Timeout
- The session Timeout is set to 36 hours -- this is the HAproxy related Timeout regarding the TCP connection
- Kerberos/OpenAFS have separate/shorter timeouts. You need to kinit && aklog when you're approaching timeout
Self defense of these servers
Rate Limiting
Usually we do utilize "fail2ban" to chase brute force attacks by bad guys trying to hack login credentials. For technical reasons this is not possible for this "haproxy" approach. The workaround is:
 |
We do limit the rate of new ssh- (tcp-) connections from any given source IP address to 1 per minute. This rate will get increased when "port knocking" is established. |

|
When you're going to login via ssh you usually have three tries to enter your password. Technically this is just one single connection! The next three tries come with the next connection, which is only possible after one minute. Trying to to log in too early gives just a generic error message:
~# ssh username@shell.stud.informatik.uni-goettingen.de ssh_exchange_identification: read: Connection reset by peer
This behavior should be fine for most users where each one has a different IP address than other people.
If you are a group of students behind NAT this could be a problem. We need yet to find out if this might be a problem for students residential establishment in Göttingen.
Port knocking
Because the above limitations still allow too many brute force attempts we need to enhance security. For this a "port knocking daemon" got installed. It works like a secret knocking sequence at the door of a conspiracy meeting.
Only after you have successfully performed that secret sequence the door is opened for a moment. In our technical context this means that the listing sshd is reachable for 30 seconds after knocking...
 |
Secret: 33778 • 22999 • 44333 | 
|
Successfully triggering is possible a variety of software tools:
Linux with knockd installed
If you are using Linux and the package knockd is actually installed (which is not a requirement!) you can use this one-liner to log in:
~$ knock shell.stud.informatik.uni-goettingen.de 33778 22999 44333 && sleep 1; ssh username@shell.stud.informatik.uni-goettingen.de
If this fails try a slower version:
~$ knock shell.stud.informatik.uni-goettingen.de 33778; knock shell.stud.informatik.uni-goettingen.de 22999; knock shell.stud.informatik.uni-goettingen.de 44333 && sleep 1; ssh username@shell.stud.informatik.uni-goettingen.de
Linux without knockd
telnet to the rescue!
~$ telnet shell.stud.informatik.uni-goettingen.de 33778 ~$ telnet shell.stud.informatik.uni-goettingen.de 22999 ~$ telnet shell.stud.informatik.uni-goettingen.de 44333 ~$ ssh username@shell.stud.informatik.uni-goettingen.de
Windows
- telnet is included in Windows also. But it is not installed by default. You need to activate it through "Windows-Features aktivieren oder deaktivieren"/"Add windows features" --> "Telnet-Client". You need Administrator privileges for this. So this is not an option on foreign computers
- There are dedicated tools available for this purpose. This one is tested and found to work as expected: https://sourceforge.net/projects/knockknock/
The zip-file contains a (surprisingly small) executable. It is usable without installation so you do not need Admin privileges
- Use a web browser to tickle those ports
OS agnostic Web Browser
Create a new folder for these bookmarks. Prepare three Bookmarks:
Of course you will end up running into a timeout as there is no webserver listening. You do not have to wait for timeout; simply cancel loading...
You can "click" them one after another. Browsers like Firefox offer a context menu entry "Alle in Tabs öffnen"/"Open all bookmarks" which tries to do what it says. You need to close all three of them one by one though.
Additionally...
If you have problems to login take a look at this page. These security aspect a definitely a work in progress and the final state is not being reached yet...
Tips 'n' Tricks
Connect to a specific machine
Circumventing the Round-Robin mechanism is possible: connect to a specific port 42000+n with n={1..6} :-)
For machine number 4:
~$ ssh -p 42004 username@shell.stud.informatik.uni-goettingen.de ####### ####### shell.stud.informatik.uni-goettingen.de - login vm: shell4.cip.loc
Todo
- Testing! -- current state considered "BETA"
- make Status Information publicly available
See also